I realize the postings have been scarce as of late, but that’s due to a lengthy bathroom renovation, which will in itself constitute a lengthy post once complete. But for now, I’ll highlight our recent vacation–the modern equivalent of a suburban slideshow:
But first, some background. As in, why would we decide to go to Williamsburg, VA? I will tell you: it was a timeshare arrangement through one of Liz’s colleagues. And no, we didn’t buy a timeshare. The time slot was gifted to us.
After perusing a list of available locations, Williamsburg won out. Partially because we hadn’t been there before, partially because it was within road trip distance for the spring break week. And I think we’ve all had enough Florida to last us a while. And, like, history and stuff!
 I’m not certain why Virginia is for lovers. And as we had the kid with us, there wasn’t an opportunity for Liz and I to figure that bit of local culture out for ourselves. I did notice that there were a lot of pull-offs with nice views, so I guess there’s a high potential for 50s-esque Lovers’ Lanes, if that’s still a thing.
I’m not certain why Virginia is for lovers. And as we had the kid with us, there wasn’t an opportunity for Liz and I to figure that bit of local culture out for ourselves. I did notice that there were a lot of pull-offs with nice views, so I guess there’s a high potential for 50s-esque Lovers’ Lanes, if that’s still a thing.
For example, take this Greenwood-Afton Rural Historic District view:

According to the sign, it’s the lowest passage through the Blue Ridge Mountains, so due to transportation implications, it’s an old town. Makes sense. Lover’s Lane indeed, had we loitered there too long and I started discussing infrastructure and logistics with Liz.
And speaking of infrastructure, check out the George P Coleman Memorial Bridge in Yorktown. Bridges!:

The next day, we got to see a naval vessel pass under it:

It was later moored up at the Naval Weapons Station further up the York river:

Okay, enough of the ship. Local history time!
For those not in the loop, Colonial America had some disagreements with the British. The particular incident at this spot in Yorktown involved an American and French siege of Admiral Nelson’s forces. The British were defeated in the engagement, and as victors tend to do, a phallus of triumph was then later erected to immortalize the event. In this case, the Yorktown Victory Monument.
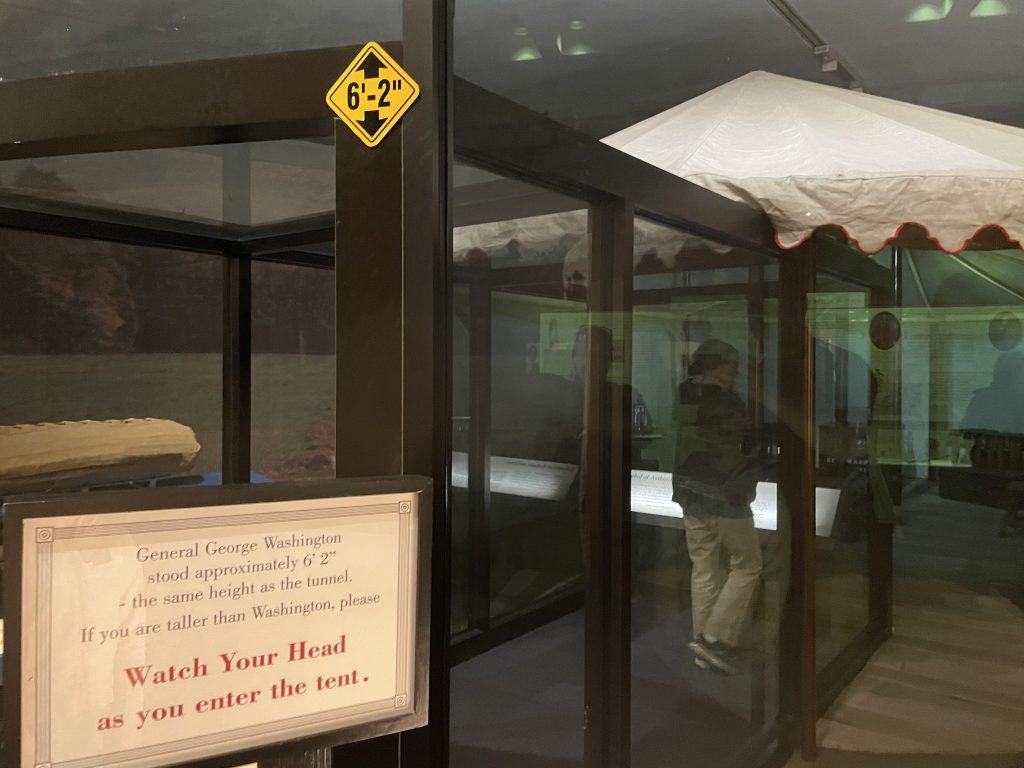
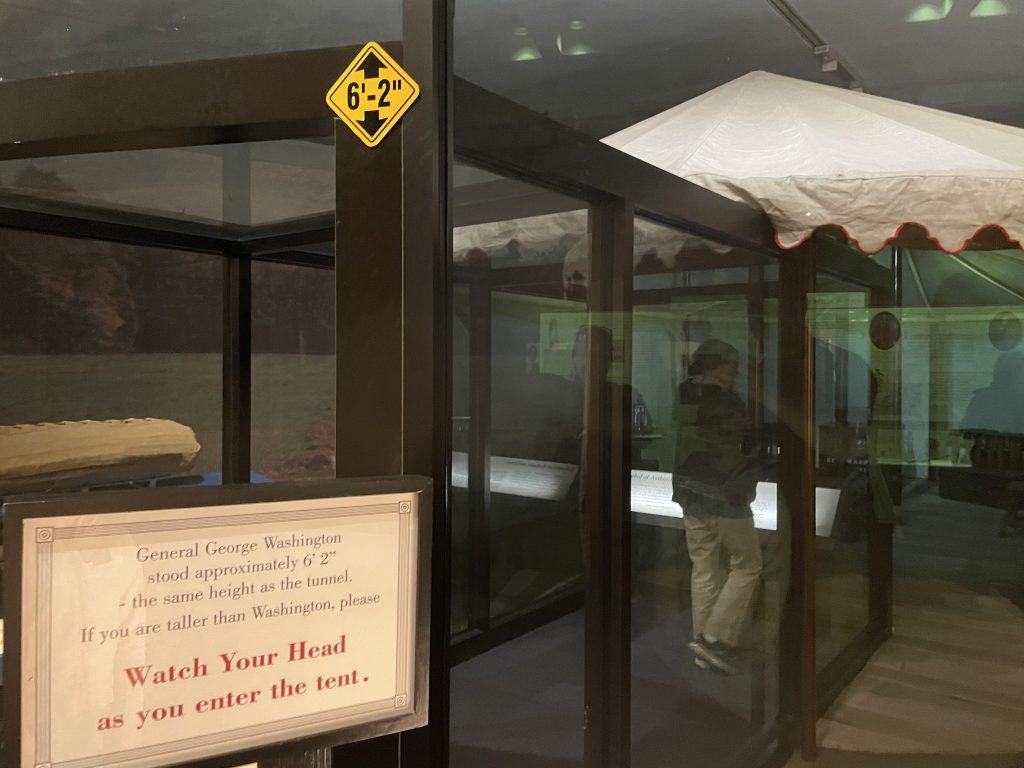
A museum at the battlefield itself has George Washington’s original tent too, which gets the place legit coolness points:
The original fortifications were mostly fenced off, but some sections were open. Here I am making the kid appreciate the effort required to storm the lines:

 And here we are enjoying some local seafood, as is mandatory when visiting the coast. They were very big on the oysters there, sporting varieties from all the major river inlets. I had never had a sampling like that before, and sure enough, they did all taste a little different. I also remember getting food poisoning the first time I ever ate them, but thought that would be an isolated occurrence. I was wrong. That night was mighty unpleasant.
And here we are enjoying some local seafood, as is mandatory when visiting the coast. They were very big on the oysters there, sporting varieties from all the major river inlets. I had never had a sampling like that before, and sure enough, they did all taste a little different. I also remember getting food poisoning the first time I ever ate them, but thought that would be an isolated occurrence. I was wrong. That night was mighty unpleasant.

The old man joined us for a couple days. His sister and that part of the clan live nearby–a happy accident as we didn’t figure that out prior to booking. It made an excuse to meet up and visit some touristy local shops along the waterfront while the kids ran around, though they didn’t fancy my idea of visiting The Great Dismal Swamp. For reference, the last time we spent time with them, Liz became known as “outdoorsy”, so they’re not exactly the type to venture too far from civilization.
We never did make it to the swamp, partially on account of my oyster problems, partially due to the distance. Instead, we chose a venue with less walking and more toilets: the Virginia Living Museum, an indoor/outdoor mini zoo and aquarium that highlighted local biology.


 But the ultimate goal was Jamestown. No history lesson needed there. That was simply a checkbox item for while we were in the area.
But the ultimate goal was Jamestown. No history lesson needed there. That was simply a checkbox item for while we were in the area.
Except we didn’t realize Jamestown Settlement and Historic Jamestown were different attractions. We ended up at the former, which was a museum with an outdoor settlement re-creation complete with replicas of the original ships.


Still cool though.
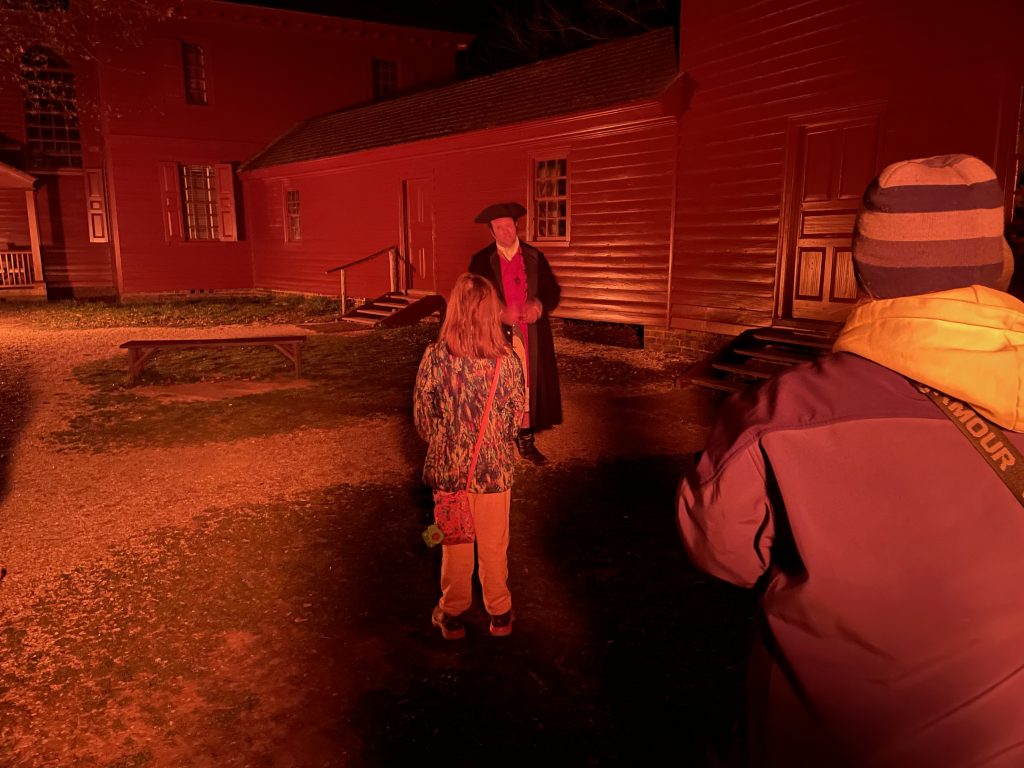
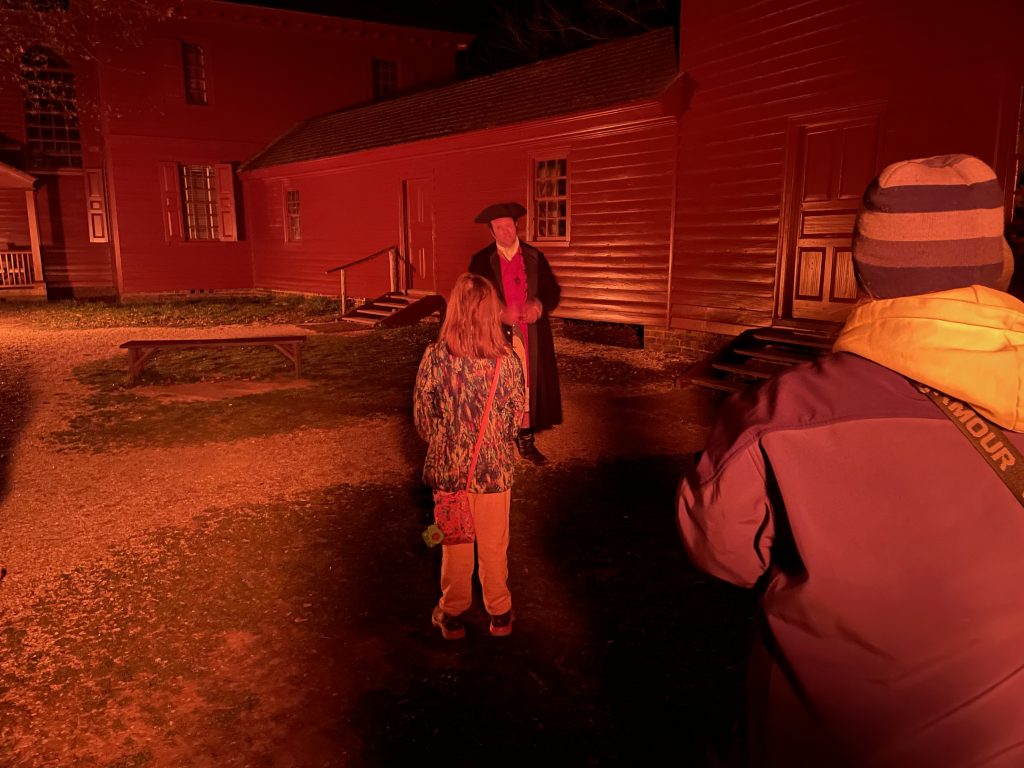
More history that night followed with a Williamsburg ghost tour. The history kind–not the try to find evidence of the flatulent supernatural kind, to be clear. Turns out the kid really likes a compelling narrative.
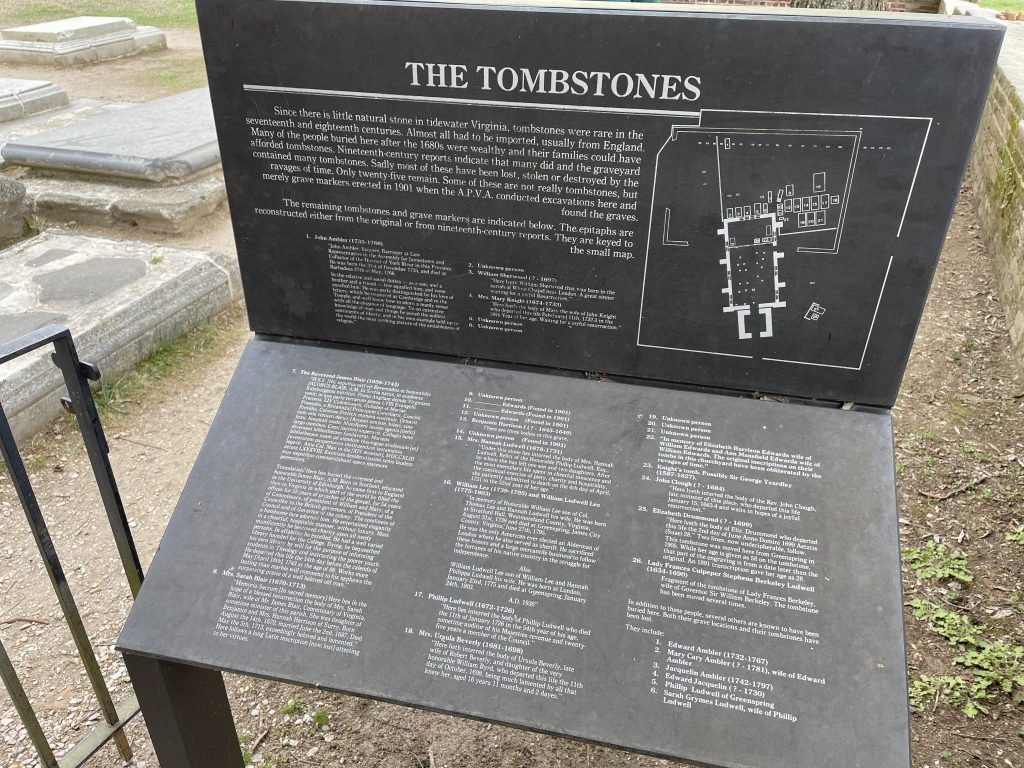
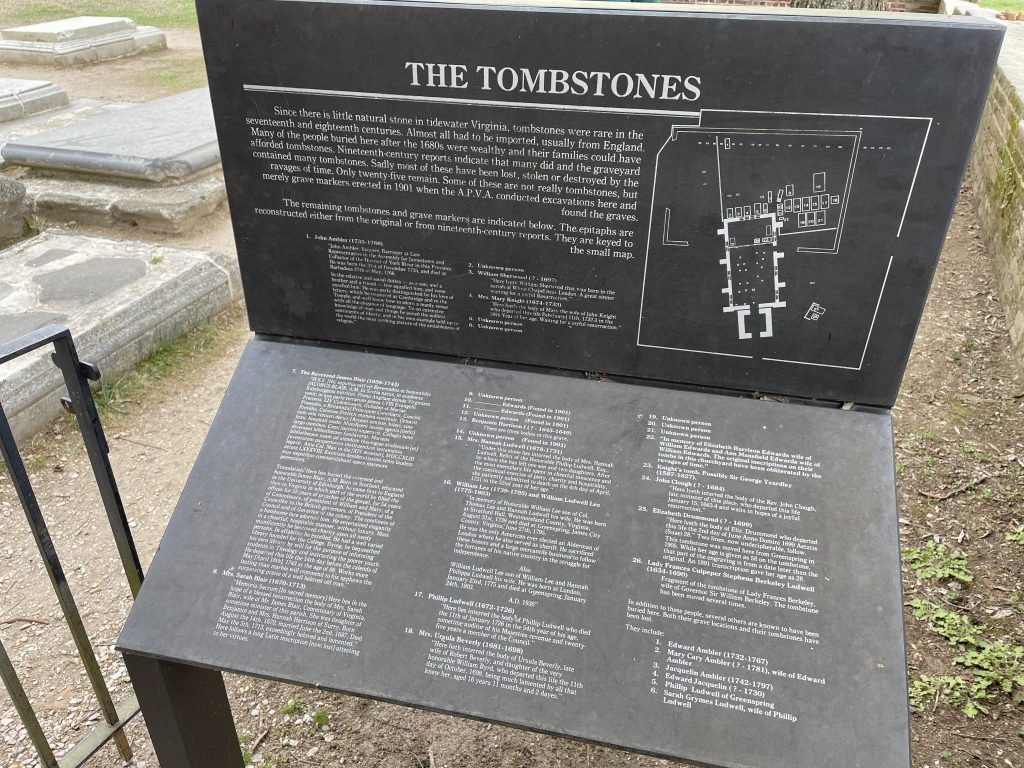
 We still made it to Jamestown, Historic Jamestown, on our final day, which included its own museum too. You’d think they’d combine some of these, except their ownership varied. Quite a racket with those tickets. But, as with Virginia’s roads having tolls, inadequate funding requires passing the bill to someone, and I’m familiar with Ohio roads and museums, so fine–I’ll pay.
We still made it to Jamestown, Historic Jamestown, on our final day, which included its own museum too. You’d think they’d combine some of these, except their ownership varied. Quite a racket with those tickets. But, as with Virginia’s roads having tolls, inadequate funding requires passing the bill to someone, and I’m familiar with Ohio roads and museums, so fine–I’ll pay.
True to form, there was another victory phallus, this one to commemorate the first “successful” English settlement in the Americas. All it took was the mass importation of unskilled colonists until some of them finally survived. Okay that’s a bit cynical, but after days of reading the history, that’s essentially what happened.





When the seat of government moved further inland, the fort was abandoned. I guess they weren’t too keen on preserving a place with that many buried bodies. Then it was assumed that the James river eroded the original land, but excavation later revealed the palisade post holes, which were used in the rebuilding. So the current fence is exactly where it was originally, with only a corner having been lost to the river. Damn cool to me. Also unsettling at how small the place was.
A path circled the local area, with all the old housing foundations. The road to the rest of the island was closed however, so we were denied the scenic tour. A lot of things were closed, presumably due to the pandemic. Oh well. We got to visit the fort. So concluded the Virginia trip.
Except for a small detour coming home. I wanted to see the New River Gorge Bridge in West Virginia, because bridges and infrastructure and such! Well, mostly because it’s just an iconic Americana image, and we didn’t have to deviate too far to see it.

Liz declined to take the scenic boardwalk down the full 876 feet. There are limits to her outdoorsy-ness.
The kid also seemed done with vacation, so I’ll conclude here with a picture of her unamused vacation face against the bridge backdrop:

Vacation 2022 done. We missed 2 years because of the pandemic. Hopefully we can still do a few more of these.
–Simon









 Good knives are important because bla bla bla steel grade tempering craftsmanship. You obviously appreciate a good quality knife because you’re super discerning with your l337 culinary skilzzz. There’s Japanese and German style knives–which are best for you? I will provide you the main differences in a cookie cutter paragraph repeated verbatim across every link on the search results first page. And here’s an arbitrary list of expensive knife manufacturers that I found online, too, with convenient links to Amazon. Of course I’ve used them all, at $100-$600,000 per blade, that’s totally believable. I swear I know what I’m talking about. I’m an expert. (We may earn a commission on the included affiliate links. And by using this site you agree to internet marketing trackers, I mean cookies, which need to be enabled for the best experience.)
Good knives are important because bla bla bla steel grade tempering craftsmanship. You obviously appreciate a good quality knife because you’re super discerning with your l337 culinary skilzzz. There’s Japanese and German style knives–which are best for you? I will provide you the main differences in a cookie cutter paragraph repeated verbatim across every link on the search results first page. And here’s an arbitrary list of expensive knife manufacturers that I found online, too, with convenient links to Amazon. Of course I’ve used them all, at $100-$600,000 per blade, that’s totally believable. I swear I know what I’m talking about. I’m an expert. (We may earn a commission on the included affiliate links. And by using this site you agree to internet marketing trackers, I mean cookies, which need to be enabled for the best experience.)
 I’m not certain why Virginia is for lovers. And as we had the kid with us, there wasn’t an opportunity for Liz and I to figure that bit of local culture out for ourselves. I did notice that there were a lot of pull-offs with nice views, so I guess there’s a high potential for 50s-esque Lovers’ Lanes, if that’s still a thing.
I’m not certain why Virginia is for lovers. And as we had the kid with us, there wasn’t an opportunity for Liz and I to figure that bit of local culture out for ourselves. I did notice that there were a lot of pull-offs with nice views, so I guess there’s a high potential for 50s-esque Lovers’ Lanes, if that’s still a thing.





 And here we are enjoying some local seafood, as is mandatory when visiting the coast. They were very big on the oysters there, sporting varieties from all the major river inlets. I had never had a sampling like that before, and sure enough, they did all taste a little different. I also remember getting food poisoning the first time I ever ate them, but thought that would be an isolated occurrence. I was wrong. That night was mighty unpleasant.
And here we are enjoying some local seafood, as is mandatory when visiting the coast. They were very big on the oysters there, sporting varieties from all the major river inlets. I had never had a sampling like that before, and sure enough, they did all taste a little different. I also remember getting food poisoning the first time I ever ate them, but thought that would be an isolated occurrence. I was wrong. That night was mighty unpleasant.


 But the ultimate goal was Jamestown. No history lesson needed there. That was simply a checkbox item for while we were in the area.
But the ultimate goal was Jamestown. No history lesson needed there. That was simply a checkbox item for while we were in the area.

 We still made it to Jamestown, Historic Jamestown, on our final day, which included its own museum too. You’d think they’d combine some of these, except their ownership varied. Quite a racket with those tickets. But, as with Virginia’s roads having tolls, inadequate funding requires passing the bill to someone, and I’m familiar with Ohio roads and museums, so fine–I’ll pay.
We still made it to Jamestown, Historic Jamestown, on our final day, which included its own museum too. You’d think they’d combine some of these, except their ownership varied. Quite a racket with those tickets. But, as with Virginia’s roads having tolls, inadequate funding requires passing the bill to someone, and I’m familiar with Ohio roads and museums, so fine–I’ll pay.