It’s not quite paranoia, but I wanted another outside camera. This time, I wanted a view of the garden. Why? Because the house doesn’t have any windows on that side and I want to check in on the veggies. And to yell at any deer and cats that trigger the motion alert (the latter of which I’ve already chased away with the camera’s alarm). I’m also hoping its presence will be a deterrent to a certain neighbor who takes their dog across the property line to shit. Doubtful.
But between the pandemic and chip shortage, the camera model I wanted, which I’ve previously installed in the backyard, hasn’t been available for a couple years now. Then, finally last month, it appeared open to order, though it must have been backordered because I only just received it over the weekend. No matter. I have it now.
Taking the previous installation’s lessons, I routed a CAT6 through the attic and to the garage window, where I installed a keystone jack, and connected to this a specially-ordered outdoor patch cable which ran along the eaves and to the camera.

I also must be losing my touch with crimping cable terminals. I struggled to the point of fury before deciding to go out and buy a different model, which worked just fine. User error maybe.
Surpassing the other camera, this is now the longest ethernet run I’ve pulled. And fortunately, it worked the first time.

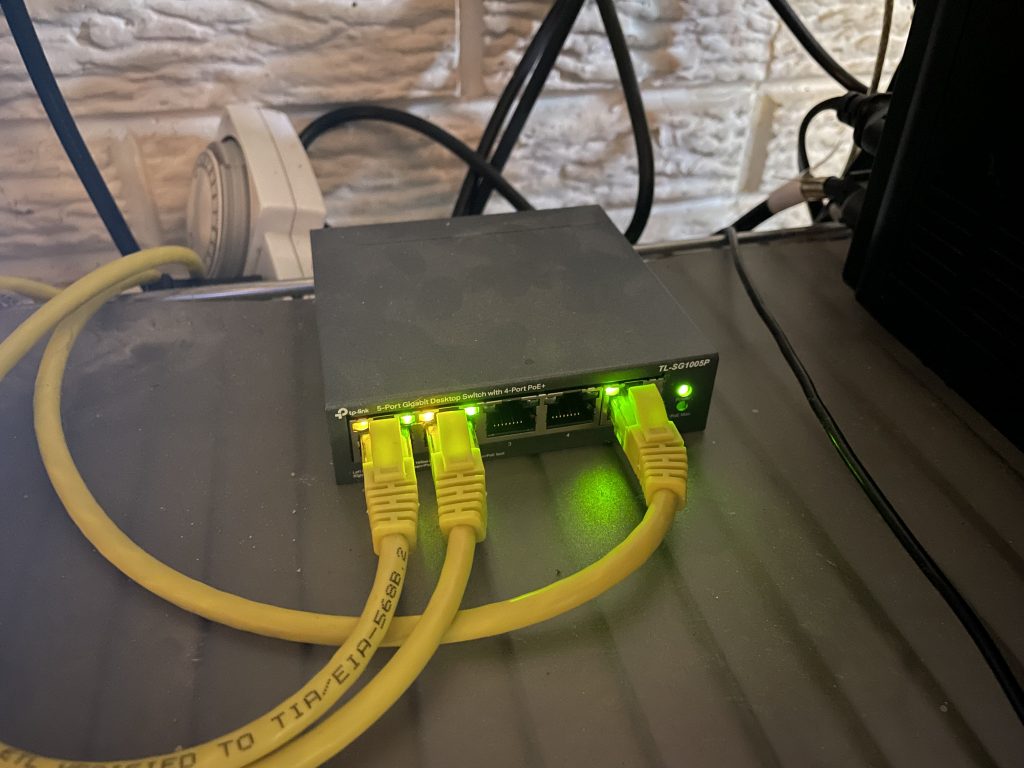
This makes my 10th drop to the patch panel. And I even acquired a PoE switch since last time, thus replacing the prior single-port injector and giving me 4 powered ports.
Looking forward to some nature pics. And foiled pooping attempts.
–Simon










